Fai-updater
fai-updater - run and supervise softupdates on many machines at the same time
Screenshots
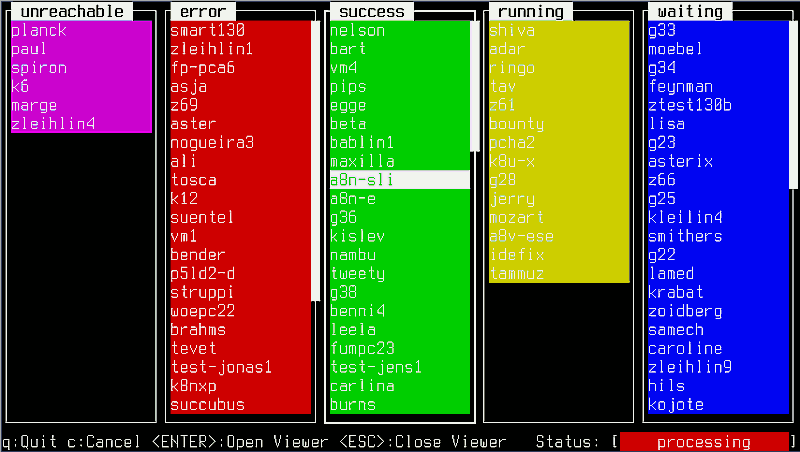
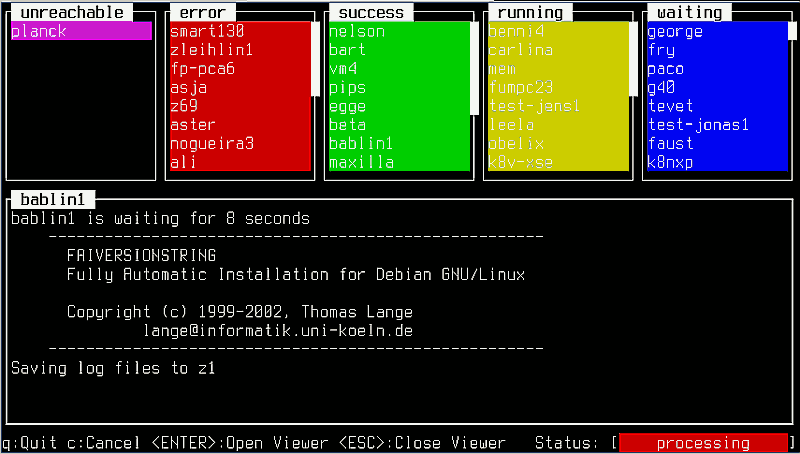
Everybody likes screenshots, so here are two. Note: they were done using fai-updater's dry-run mode, which does not touch the hosts, but feeds fai-updater with random log snippets instead to test the updaters log parser.
General logic is the following:
- clients are put into the "waiting" queue (the right column), by default in randomized order
- as soon as a slot in the "running" queue gets free (the second column from the right), the first "waiting" client gets updated/put into the "running" status and stays there until the update task finished
- Depending on the outcome, the client is sorted in one of the first three columns:
- Unreachable: the host was unreachable or the fai softupdate could not be started there
- Error: the updater detected an error during the update (basically, it parses for the error string produced by a logcheck script such as hooks/savelog.LAST in the simple example)
- Success: the update finished and no error was detected
Fai-updater in its basic mode
Fai-updater with an open logfile viewer
License
I put this code under the GPLv2
Download
Until I figure out how to upload a tarball to the wiki, you can download fai-updater from [1] File:Fai-updater-20060321.tgz
Required packages
for the frontend, you need the Curses::UI perl module, in Debian you get it via
apt-get install libcurses-ui-perl
On the client side, fai-client is needed and of course a FAI configuration which is update-safe.
Install
Just unpack the tarball.
Command line options
updater-curses [options] <netgroup|-H host1,host2,...>
--help display this help message
--version print version
-o ordered mode: don't randomize order of hosts
-s <number> number of updates running simultanously
-n dryrun mode: use a dummy-script instead of really
contacting the clients
Connecting to the clients
A script using ssh is included, but of course you can edit it to match your own needs.
To be able to connect to the clients using the provided libexec/faiupdate, you need to have some way to access them via ssh as root without entering a password.
A solution for this is to install a matching file as /root/.ssh/authorized_keys, start ssh-agent and load the private key into it _before_ starting fai-updater.
Another, but from a security point of view dangerous, possibility is to use a passphrase-less ssh private key into the account under which you run fai-updater.
Some comments on the code
I know the code is quite rough, as though I tried programming cleanly, a lot of hacks have slipped in, and I don't have the time to clean up the code right now due to my diploma thesis' deadline ;)
If you have any questions or suggestions, feel free to write me.
Henning Glawe <glaweh (at) debian (dot) org>